Cyberthreats from U.S. adversaries are spurring innovative American countermeasures to help protect against potentially devastating attacks targeting U.S. government agencies and private sector organizations.
Microsoft (NASDAQ:MSFT) recently won an important 10-year contract worth up to $10 billion to help the U.S. Department of Defense (DoD) and its partner organizations defend against cyberattacks from American adversaries that increasingly include other countries and their agents. The risk of cyberattacks is on the rise and the stakes are heightening to counter such threats.
The U.S. Cyber Command, also known as CYBERCOM, is spearheading the DoD’s electronic countermeasures aimed at protecting against the most advanced cyberattacks. Established in May 2018, CYBERCOM’s key role led to its elevation to gain unified combatant command status with a mission that includes creating powerful offensive threats, if needed.
New Cyberthreats from U.S. Adversaries Led DoD to Create CYBERCOM
The critical need to respond to escalating cybersecurity threats from across the globe led the DoD to give official recognition to cyberspace as a warfighting domain in 2004. Cybersecurity also now is part of the U.S. National Defense Strategy.
The first stock every investor should buy to profit from the most fruitful research and development (R&D) in cybersecurity defense is one of the biggest, Redmond, Washington-based Microsoft, which will be running the Pentagon cloud, said Hilary Kramer, host of a national radio program called “Millionaire Maker.” Kramer, who also heads the 2-Day Trader service that has netted profits in 22 of its first 28 trades for an average return of 11.04 percent, said the Microsoft contract is worth $1 billion a year over the next decade.
That annual revenue stream will be enough to keep the giant software company’s growth needle moving for the foreseeable future, said Kramer, who just finished a new book, “GameChanger Investing,” and launched the IPO Edge trading service on Dec. 10. More importantly, the huge long-term contract locks competitors out of the DoD platform, she added.
Microsoft won the firm-fixed-price contract on Oct. 25 totaling $10 billion, if all options during its 10-year length are exercised. The Joint Enterprise Defense Infrastructure (JEDI) Cloud contract will provide enterprise level, commercial Infrastructure as a Service (IaaS) and Platform as a Service (PaaS) to support DoD business and mission operations. Funds of $1 billion will cover the minimum guarantee for fiscal year 2020. The expected completion date of the 10-year pact is Oct. 24, 2029.
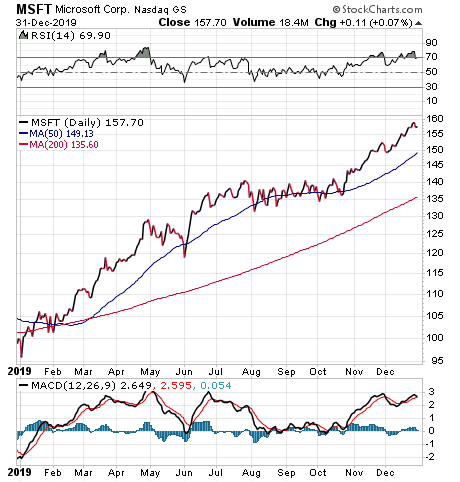
Chart courtesy of www.stockcharts.com
“Think about it,” Kramer continued. “If all the office systems are integrated into a Microsoft environment, they’re going to work better with the security and partners Microsoft picks out. An outside contractor is really going to need to fight to get any traction at all. If they’re smart, they’ll simply go straight to Microsoft and lobby for a place on the platform.”

Paul Dykewicz interviews New York-based money manager Hilary Kramer.
Microsoft, which also offers investors a dividend yield of 1.28 percent, already has its own cloud security tools and has assembled an impressive list of partners, said Kramer, who also heads the Turbo Trader, High Octane Trader and Inner Circle advisory services. Those Microsoft partners include: Check Point (NASDAQ:CHKP), F5 Networks (NASDAQ:FFIV), Palo Alto Networks (NYSE:PANW), Fortinet (NASDAQ:FTNT) and especially the Symantec assets that Broadcom (NASDAQ:AVGO) bought in August, she added.
“A little win for Microsoft is a big win for Symantec,” said Kramer, who also leads the GameChangers advisory service that has booked 33 profitable trades in its last 39 closed positions. “If you’re looking for a pure play on the Pentagon cloud, AVGO is probably as close as it gets.”
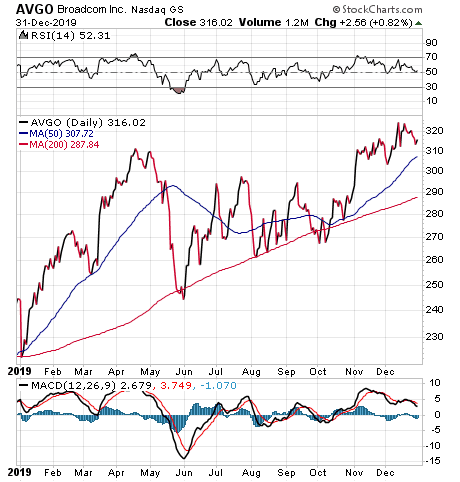
Chart courtesy of www.stockcharts.com
Fund Focuses on Cybersecurity Ingenuity to Thwart U.S. Adversaries
“A conservative but profitable way to invest in cybersecurity is through the fund ETFMG Prime Cyber Security (NYSEARCA:HACK),” said Bob Carlson, who leads the Retirement Watch investment advisory service.
The exchange-traded fund, launched in 2014, holds technology stocks, but has trailed broad technology indexes during bull markets, Carlson said.
“The fund so far has had good defensive characteristics,” Carlson continued. “It had a positive return in 2018 of 6.72%, when most stocks and especially technology stocks were down for the year.”
Top holdings in the fund include Sophos Group PLC (NASDAQ:SPHHF), Carbonite (NASDAQ:CARB), Splunk (NASDAQ:SPLK), Fortinet (NASDAQ:FTNT) and Avast (NASDAQ:AVST). The ETF holds 56 stocks and many of them each account for 3 percent of its portfolio. About 10 percent of the stocks are European, 5 percent are Asian and the rest of the portfolio is composed of U.S. companies.
“The ETF is thinly traded, so be careful when purchasing,” Carlson cautioned. “Set a purchase price limit instead of putting in a market order. You don’t want a short-term surge in buying to push your purchase price artificially higher.”
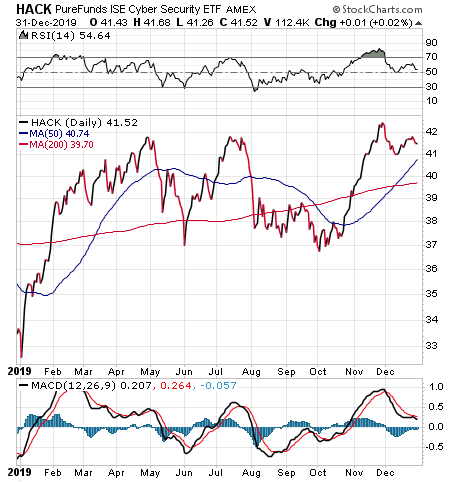
Chart courtesy of www.stockcharts.com
Department of Homeland Security Teams up with Cyber Companies
Today, 11 federal government agencies and more than 60 private sector communications and information technology companies share critical communications information and advice with the U.S. Department of Homeland Security. The collaboration supports the national security and emergency preparedness communications mission of the Department of Homeland Security’s Cybersecurity and Infrastructure Security Agency (CISA).
The CISA is the Department of Homeland Security’s focal point for sharing cyberthreat indicators and information. Another responsibility of the CISA is to provide tools, services and programs to reduce and mitigate the risk of catastrophic consequences from cyberattacks.
“By bringing together all levels of government, the private sector, international partners and the public, CISA strengthens the resilience of our nation’s critical infrastructure,” said Jeanette Manfra, assistant director for Cybersecurity at CISA in the Department of Homeland Security. She spoke on Sept. 10, 2019, before the House Armed Services Committee’s Subcommittee on Intelligence and Emerging Threats and Capabilities, as well as the Committee on Oversight and Reform, and its Subcommittee on National Security. Manfra addressed the “Role of the United States government in Securing the Nation’s Internet Architecture.”
“Our adversaries have been developing and using advanced cyber capabilities in attempts to undermine critical infrastructure, target our livelihoods and innovation, steal our national security secrets and threaten our democratic institutions,” Manfra said.
Virtually every element of modern life now is dependent on cyber infrastructure, which encompasses routing and switching software, operational support systems and user applications, Manfra testified.
Cyberthreats from U.S. Adversaries Imperil American Spacecraft
Former National Security Advisor John Bolton stated publicly that the United States has expanded operations to counter digital espionage and other commercial hacks. In June 2019, Bolton said America is “opening the aperture” and broadening the areas of space it intends to defend.
As I reported in May 2019, Vice President Pence told attendees during his speech at SATELLITE 2019 in Washington, D.C., that countries actively are pursuing weapons to “jam, blind and disable” U.S. communications satellites via electronic attacks.
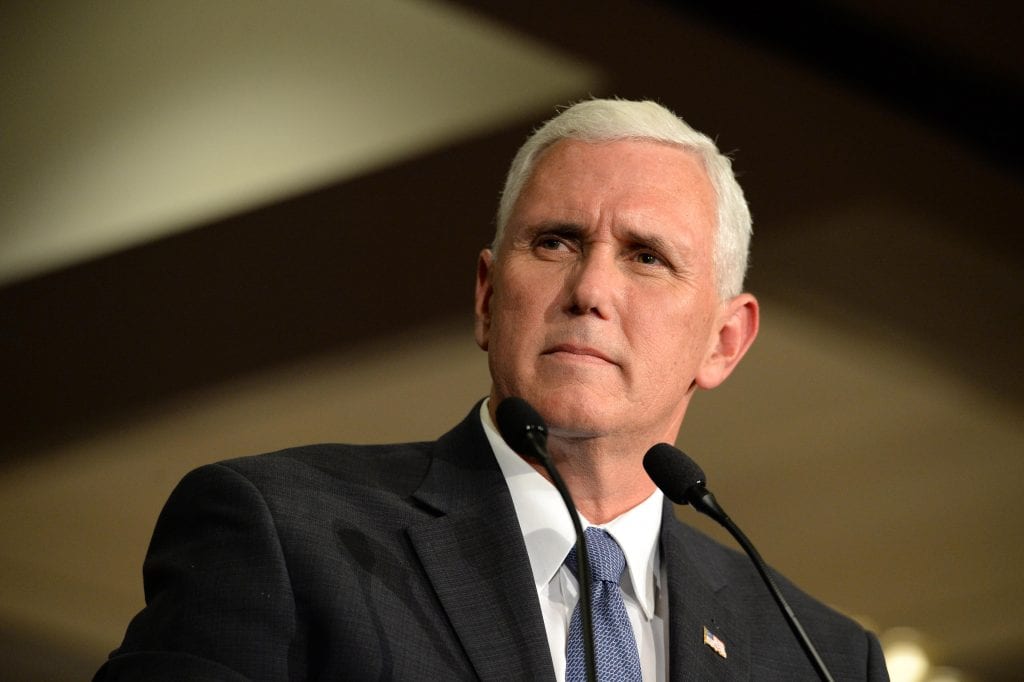
Vice President Mike Pence
“We are working in a multi-domain, whole-of-government approach, as well as with a broad spectrum of industry partners, to ensure that we are meeting and staying ahead of any threat posed by our adversaries,” said Lt. Col. Christina Hoggatt, a public affairs officer with the U.S. Space Command. “One way we do this is through the Schriever Wargame series.”
This wargame initiative is a combined effort of the DoD, allied partners (Australia, Canada, France, Germany, Japan, New Zealand and the United Kingdom) and commercial partners to define dangerous actions and reinforce responsible behavior in space through policy and law. A wargame allows U.S. Space Command to visualize and develop common architectures to fight more effectively in future conflicts and inform people, processes and technologies to advance its joint operational missions. Wargames also let allied space-faring nations explore opportunities and challenges of national, commercial and coalition architectures to synchronize efforts that protect and defend their space operations.
Russia, China, Iran and North Korea ‘Weaponize’ Cyber Technology
Emerging cyberthreats from “sophisticated nation-state actors” such as Russia, China, Iran and North Korea already have “weaponized new technologies” to disrupt America’s democracy, compromise its national security and undermine its economy, said Rep. Cedric Richmond, D-Louisiana, who chairs the House Committee on Homeland Security’s Cybersecurity, Infrastructure Protection and Innovation Subcommittee. Rep. Richmond warned in his opening statement at an Oct. 22 hearing that such cyber technology advances enhance the capability of combative foreign governments to harm the United States.

Rep. Cedric Richmond
Rep. Bennie G. Thompson, D-Mississippi, chairman of the House Committee on Homeland Security, advised at the same hearing that emerging cyberthreats from U.S. adversaries against America are evolving and growing.
“As new networked devices and information technologies entered the marketplace, many became so mesmerized by their potential for good that we failed to appreciate and plan for the security consequences,” Chairman Thompson opined. “Although I am encouraged that we are having more conversations about the nexus between technology and security today, there is still much to be done.”
Cyberthreats Now Come from Attackers Seeking to Hide Their Identity
Specifically, Chairman Thompson recalled when the House Committee on Homeland Security came into existence on Jan. 4, 2005, it focused on defending against physical attacks by terrorists who would claim responsibility for their actions. Now, cyberthreats come from “state and non-state actors” who use cyber tools secretly to carry out attacks, blur attribution and seek to evade consequences for their actions, he added.
In December 2018, the DoD, the Department of Homeland Security, the State Department and the Office of the Director of National Intelligence identified internet of things (IoT) devices, artificial intelligence (AI) and quantum technologies as emerging, dual-use technologies that pose a threat to U.S. national security. A month later, then-Director of National Intelligence Dan Coats warned that “our adversaries and strategic competitors will increasingly use cyber capabilities,” including cyber espionage, attack and influence, to seek military, political and economic advantage over the United States, its allies and their partners.
Unfortunately, the threat cited by Coats has arrived, Chairman Thompson cautioned.
“We know that Russia has relied on its cyber capabilities to carry out influence campaigns designed to divide Americans and swing elections,” Chairman Thompson stated. “Its efforts to manipulate Americans on social media platforms were widespread, but technologically simple. I worry about the influence campaign of the future, where Russia uses AI to create ‘deepfakes,‘ that make it nearly impossible to discern fact from fiction.”
Deepfakes are manipulated videos, or other digital visuals, produced by sophisticated artificial intelligence to create fabricated images and sounds that seem real.
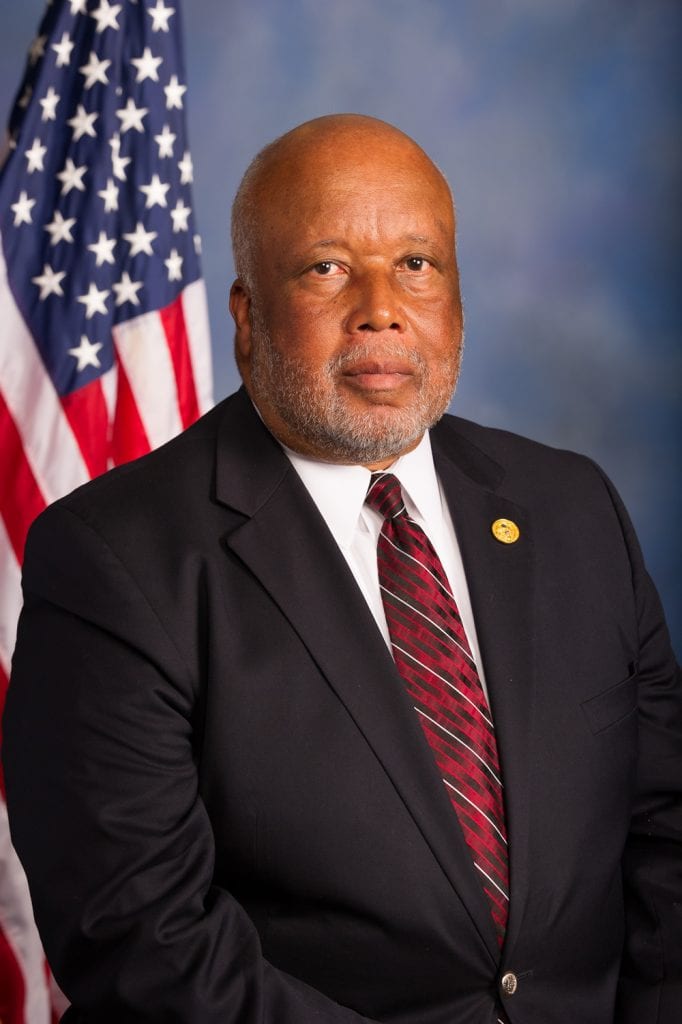
Rep. Bennie G. Thompson
China has engaged in intelligence-gathering and “economic espionage,” as well as successfully breached the Office of Personnel Management (OPM), Navy contractors and non-government entities from hotels to research institutions, Chairman Thompson continued. Further, China is investing heavily in developing quantum computing capabilities, which could undermine the security value of encryption within the next decade, he added.
Iran and North Korea Inflict Cyberattacks on America
“Over the past year, the Department of Justice has indicted two Iranians for their role in the ransomware attack against the City of Atlanta, and Microsoft recently revealed that Iran had attempted to breach a presidential campaign,” Chairman Thompson cautioned. “And according to the UN Security Council, North Korea has used its cyber capabilities to evade sanctions, stealing $670 million in various foreign and cryptocurrencies between 2015 and 2018. The momentum Russia, China, Iran and North Korea have demonstrated related to their use of cyber tools shows no signs of slowing.”
America must prepare to harness the security, economic and health care benefits of emerging technologies like AI and quantum computing, while defending against adversaries who seek to use technology to attack the United States, Chairman Thompson stated. But the government cannot do it alone, he added.
The importance of the private sector in aiding the U.S. government in protecting against cyberattacks was reflected when the Senate Committee on Homeland Security and Governmental Affairs held a roundtable meeting for members and their staff last May 15, titled “Cybersecurity Roles and Responsibilities: Private Sector Perspectives.”
In an example of bipartisanship, Sen. Ron Johnson (R-Wisconsin) and Sen. Gary C. Peters (D-Michigan), chairman and ranking member of the Senate Homeland Security and Governmental Affairs Committee, respectively, invited committee members and staff to enhance their understanding of the private sector’s view of the roles and responsibilities of federal agencies. The meeting also addressed the challenges of public-private collaboration to share information, to respond to cyber incidents and to defend critical infrastructure against cyberthreats.
Lockheed Martin Is Helping the Pentagon Defend against Cyberthreats
As the U.S. and international governments continue to focus on and invest in cybersecurity, Lockheed Martin (NYSE:LMT) provides important national defense capabilities across all five military domains — cyber, space, ground, maritime and air. These capabilities include state-of-the-art ranges, systems, architectures, tools and analytics for government agencies, the intelligence community, joint commands and military services.
As a founding member of the U.S. National Security Council’s newly formed Space Information Sharing and Analysis Center (ISAC), cybersecurity remains a growing part of the services Lockheed Martin delivers to government customers, a company spokesman said. Lockheed Martin also offers investors a current dividend yield of 2.44 percent.
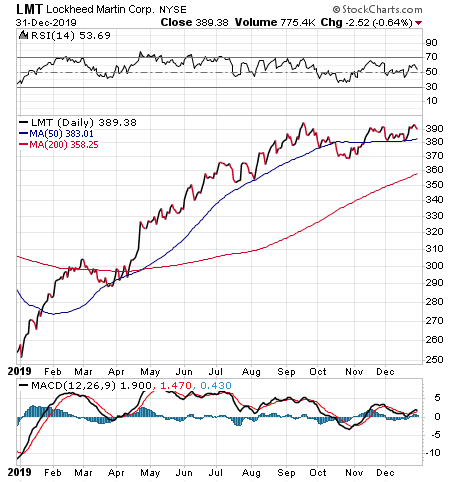
Chart courtesy of www.stockcharts.com
Artificial Intelligence Offers Promise and Peril Amid Cyberthreats
China, a serious strategic competitor of the United States, declared plans to become the world’s artificial intelligence leader by 2030 to challenge America’s military and economic position in Asia and beyond, according to the National Security Commission on Artificial Intelligence. The commission released a report in November 2019 that stated it is reasonable to conclude that AI-enabled capabilities could be used to threaten critical U.S. infrastructure, amplify disinformation campaigns and wage war.
“China has deployed AI to advance an autocratic agenda, and to commit human rights violations, setting an example that other authoritarian regimes will be quick to adopt and that will be increasingly difficult to counteract,” according to the National Security Commission.
In addition, the Defense Advanced Research Projects Agency (DARPA), which funds projects for the U.S. military, announced in September 2018 a multi-year investment of more than $2 billion in new and existing programs called “Next AI.” Goals include automating critical DoD business processes, such as security clearance vetting and accrediting software systems; improving the reliability of AI systems; enhancing the security and resiliency of machine learning; and pioneering next-generation AI algorithms and applications.
Machine learning is the most powerful artificial intelligence tool in existence today, but systems that use it can be “duped” easily by changes to inputs that would never fool a human, according to DARPA. Data used to train such systems can be corrupted and the software itself is vulnerable to cyberattack.
DARPA also began a $1.5 billion, three-year program known as the Electronics Resurgence Initiative (ERI) to support work on advancing computer chip technology. An Artificial Intelligence Exploration (AIE) program, first announced by DARPA in July 2018 and renewed in August 2019, is involved with a series of high-risk, high-payoff projects where researchers work to establish the feasibility of new AI concepts within 18 months of award.
Private Sector Fortifies U.S. National Security
Privately held Analytical Graphics Inc., of Exton, Pennsylvania, provides commercial software for designing, developing and operating aerospace and national security missions. It seeks to protect against in-orbit collisions, radio frequency interference (RFI) and the actions of U.S. adversaries that pose risks to U.S. space assets.
National security threats in space include a growing number of foreign satellites and non-space assets that seem designed for intelligence gathering, counterspace technology testing and radio frequency interference. Two examples are a pair of Russian intelligence and data-gathering spacecraft.
One is a Russian Luch spacecraft that has moved unusually close to various Intelsat (NYSE:I) satellites. Another example is a top-secret Russian military spacecraft launched on Nov. 25 to scope out other in-orbit satellites. However, the security risk to American in-orbit assets and their data is not limited to Russia’s roving intelligence-gathering spacecraft.
China’s highly maneuverable and experimental Shijian 17 (SJ-17) and its early-warning military TJS series satellites also have drawn the attention of space experts who are monitoring their movements in geostationary orbit roughly 22,236 miles above the Earth. The TJS series includes the TJS 3 spacecraft that launched in December 2018 and released a small satellite after reaching orbit, even though China never has acknowledged doing it.
The world’s most populous nation also launched a TJS 4 satellite into space on Oct. 19, 2019 to let its military test communications technologies. The TJS 4 spacecraft appears designed to complement the Chinese maritime surveillance system that grows larger every year to bring China increasingly close to military and technological parity with the United States.
Counterspace Operations of Russia and China Test U.S. Cybersecurity
Russia and China are aggressively pursuing so-called “counterspace operations” that are conducted to deny, degrade, disable or destroy an opposing side’s space capabilities. This activity includes attacks against ground-based and space-based assets using kinetic and non-kinetic methods. Such counterspace operations include offensive and defensive actions in space against an adversary’s in-orbit assets, but also air, ground and naval operations against spacecraft.
Documented cyberattacks waged by China against the U.S. government occurred in 2012 with a computer network takeover of the Jet Propulsion Laboratory (JPL). The attack gave China temporary “full functional control” of JPL networks.
In addition, China engaged in a 2014 computer network attack against the U.S. Department of Commerce’s National Oceanic and Atmospheric Administration (NOAA). Further Chinese cyber actions against a foreign government came in 2017 with a computer network attack against Indian satellite communications and again in 2018 when China targeted satellite operators, defense contractors and telecommunication companies.
The potential damage from cyberattacks could be catastrophic. As a result, the government and private sector are partnering to use American ingenuity to defend against potentially devastating damage to U.S. infrastructure, its economy, its values and its freedom.
Paul Dykewicz, www.pauldykewicz.com, is an accomplished, award-winning journalist who has written for Dow Jones, the Wall Street Journal, Investor’s Business Daily, USA Today, the Journal of Commerce, Seeking Alpha, GuruFocus and other publications and websites. Paul is the editor of StockInvestor.com and DividendInvestor.com, a writer for both websites and a columnist. He further is the editorial director of Eagle Financial Publications in Washington, D.C., where he edits monthly investment newsletters, time-sensitive trading alerts, free e-letters and other investment reports. Paul previously served as business editor of Baltimore’s Daily Record newspaper. Paul also is the author of an inspirational book, “Holy Smokes! Golden Guidance from Notre Dame’s Championship Chaplain,” with a foreword by former national championship-winning football coach Lou Holtz. Follow Paul on Twitter @PaulDykewicz.